analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
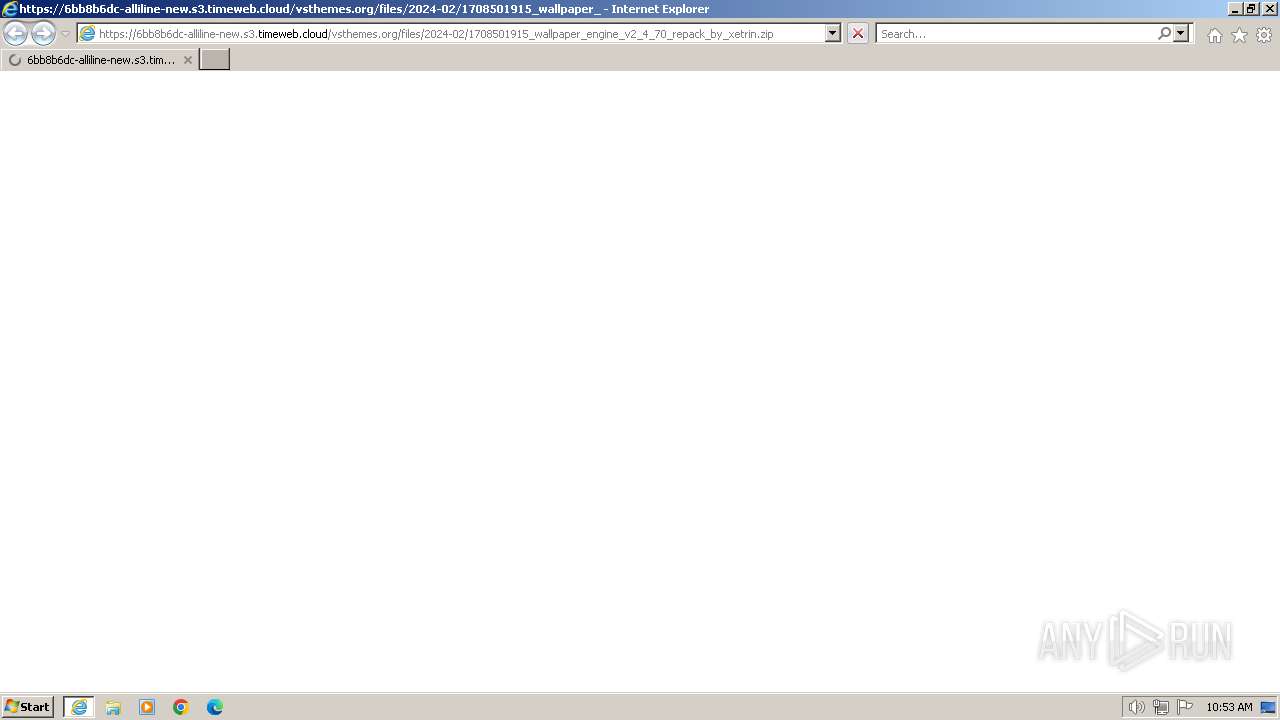
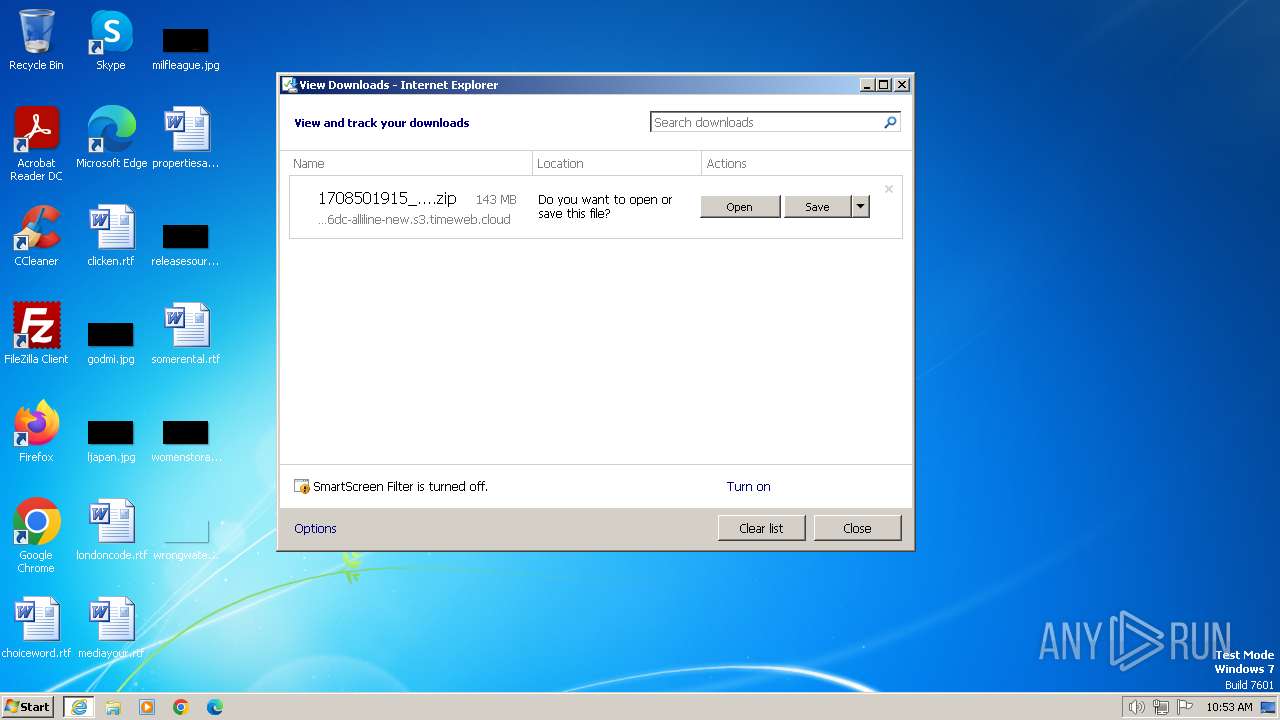
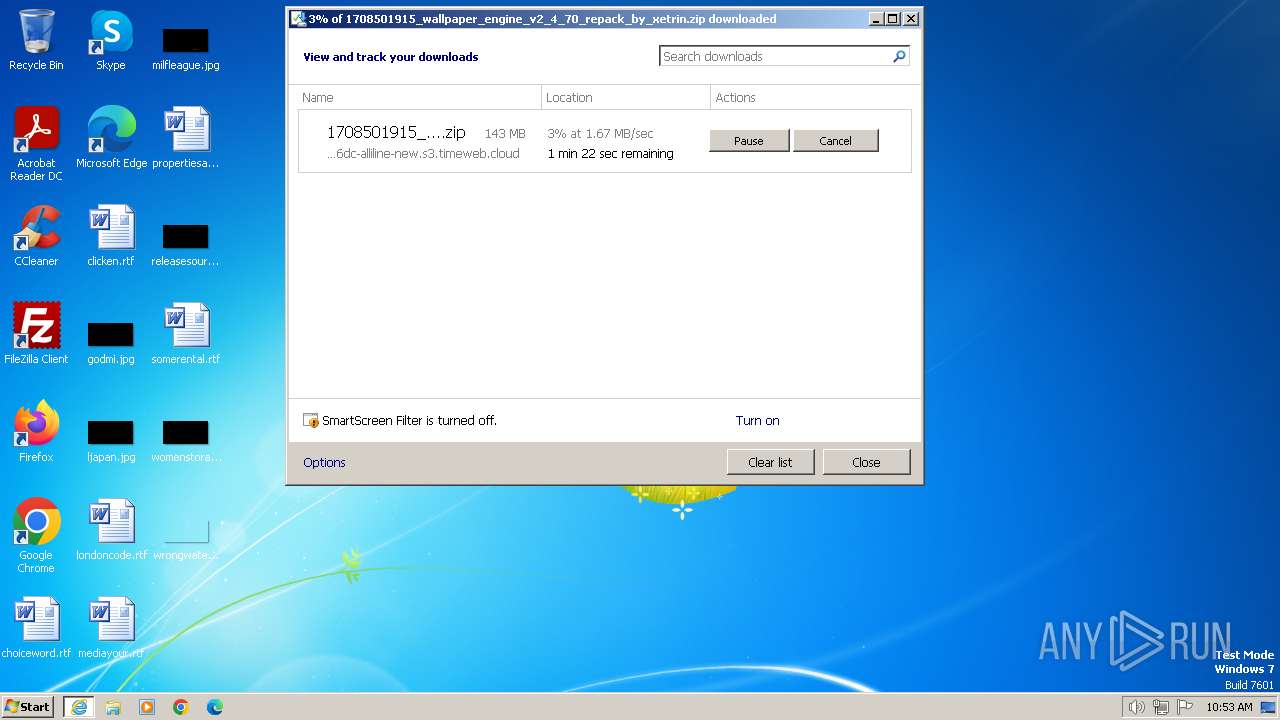
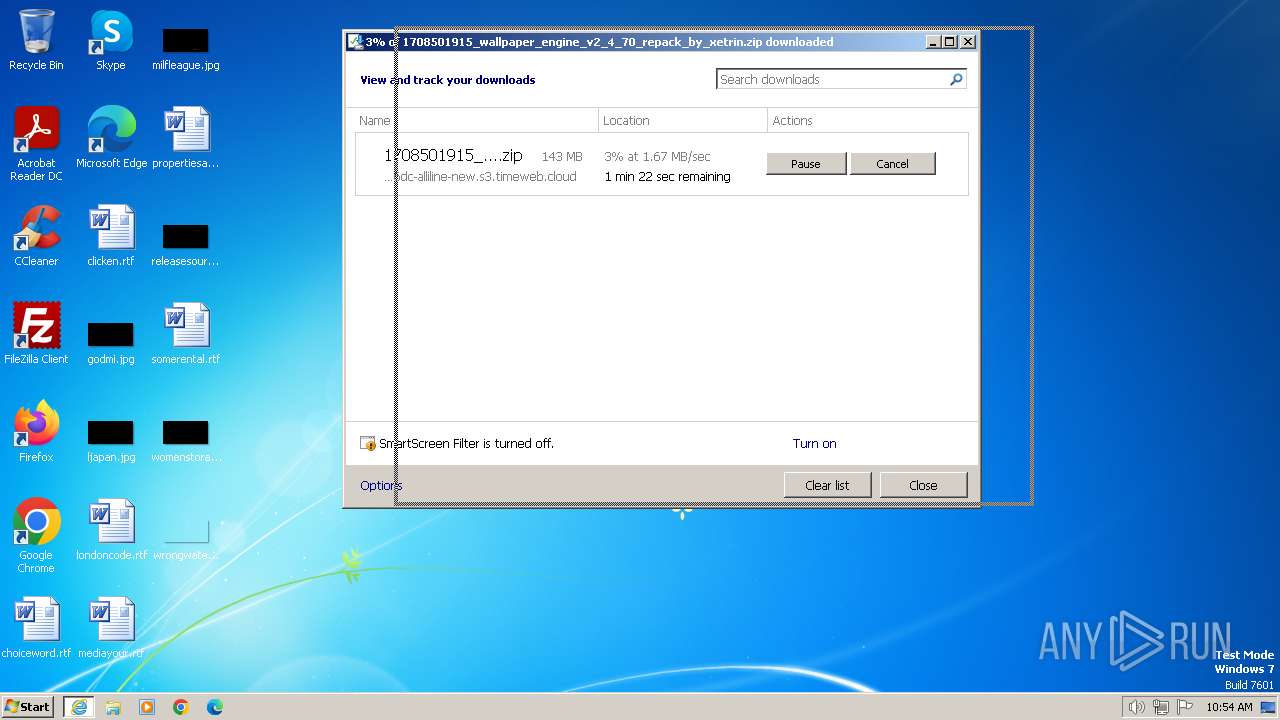
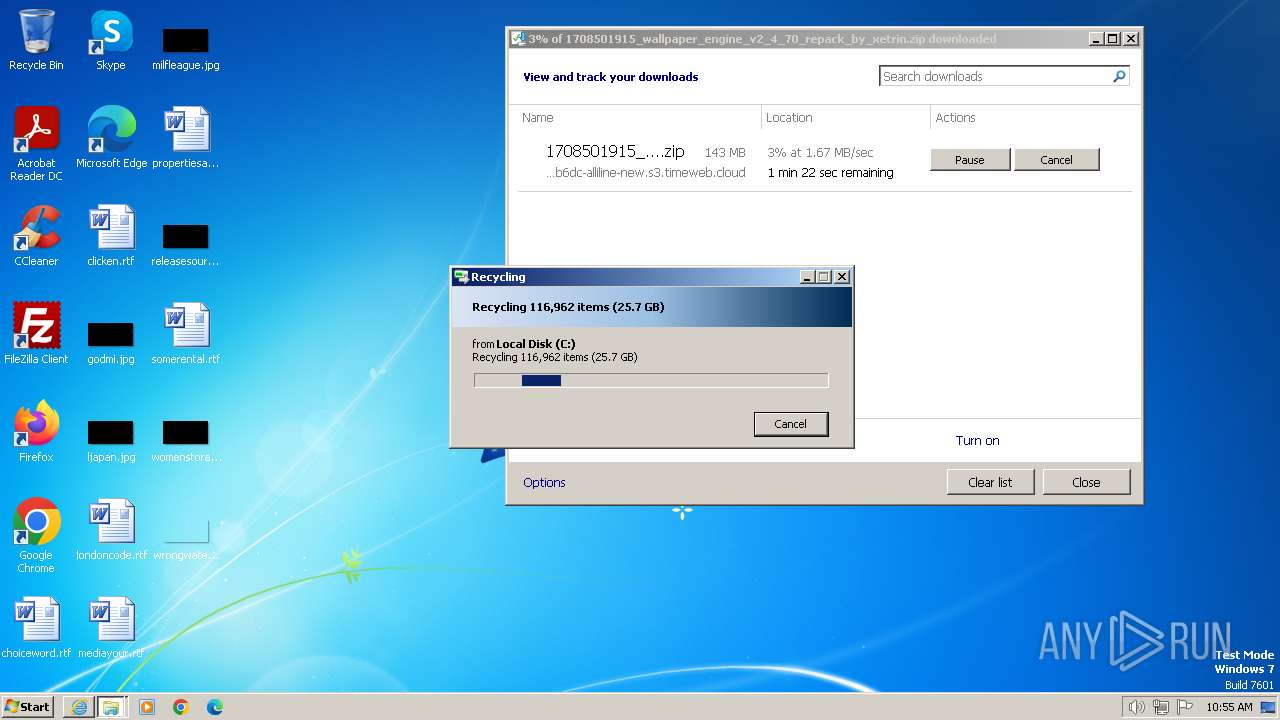
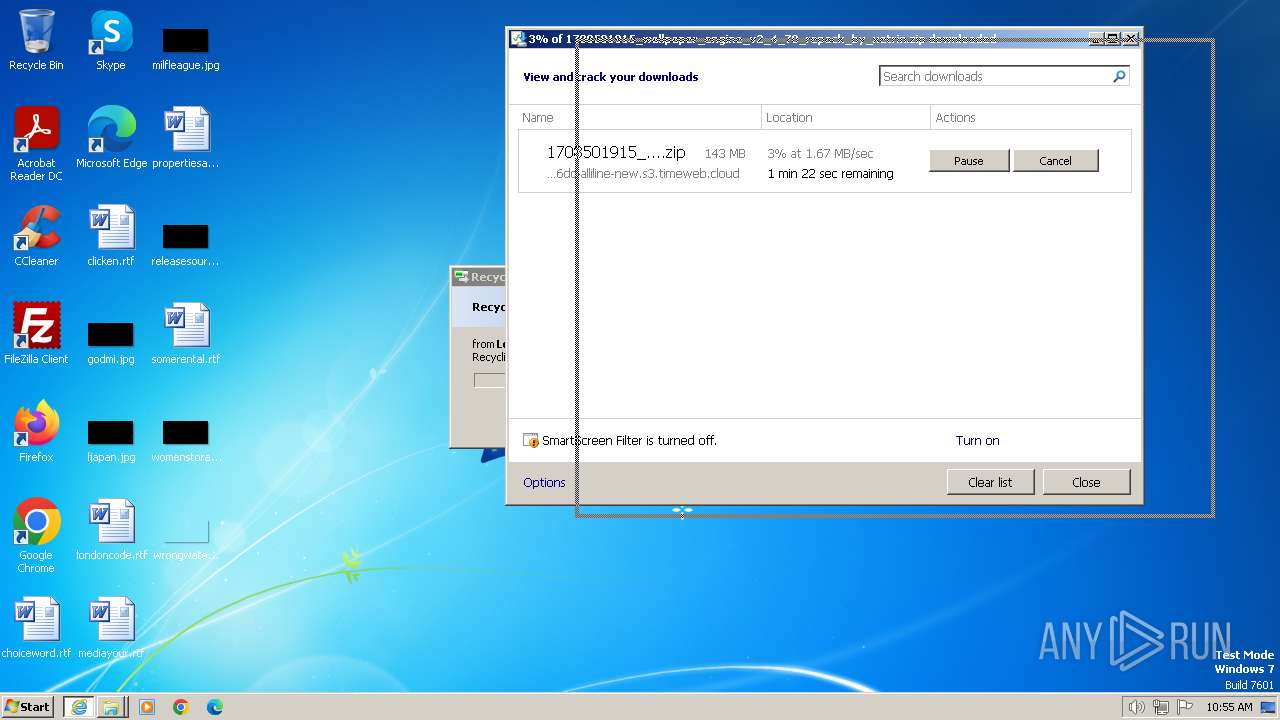
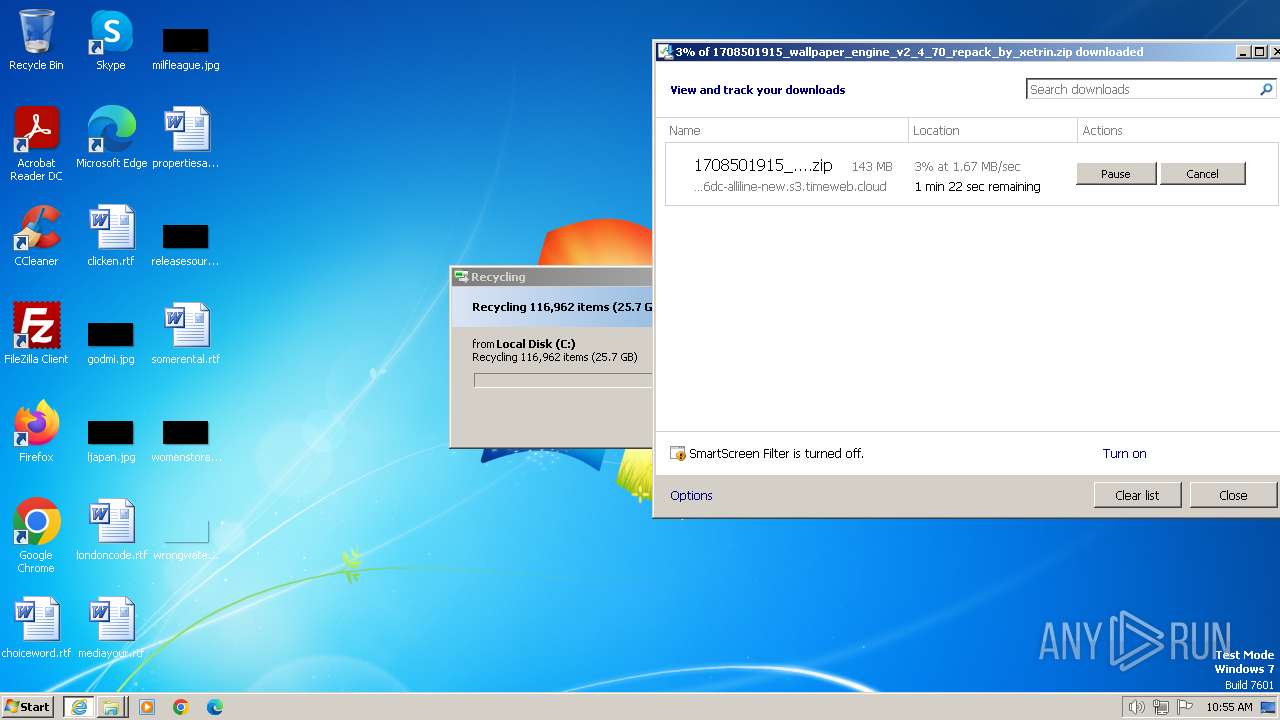
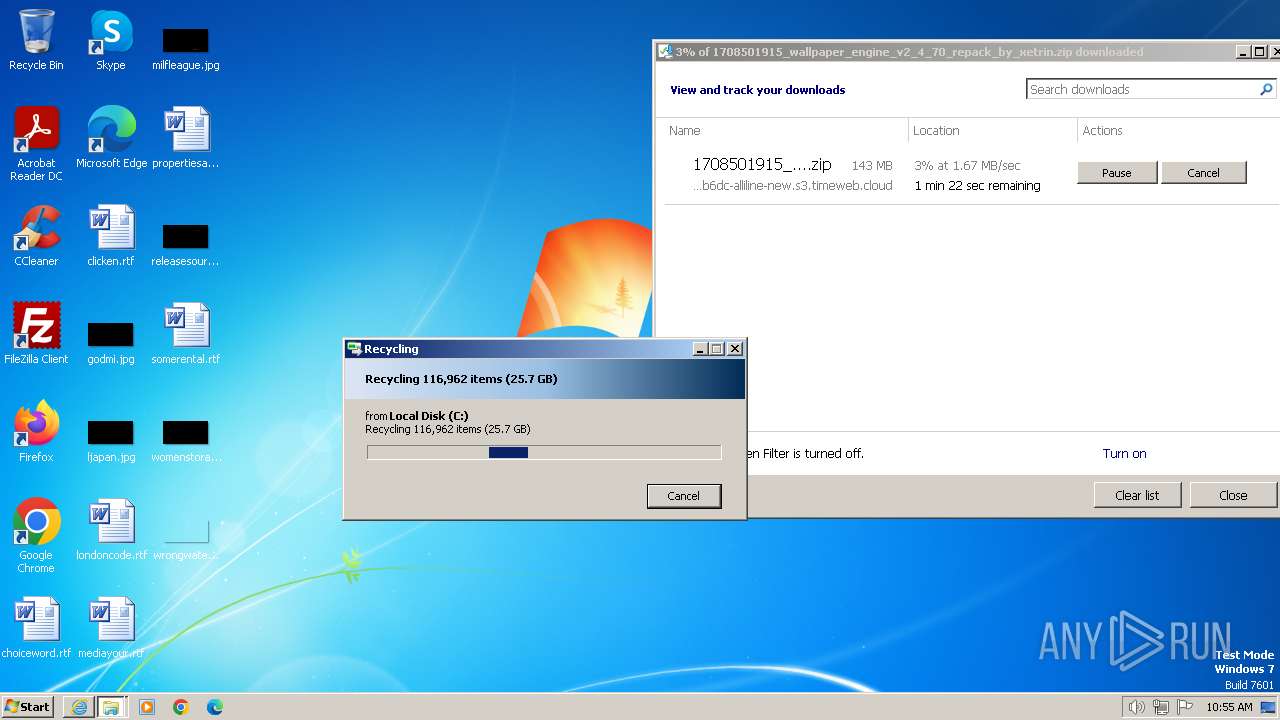
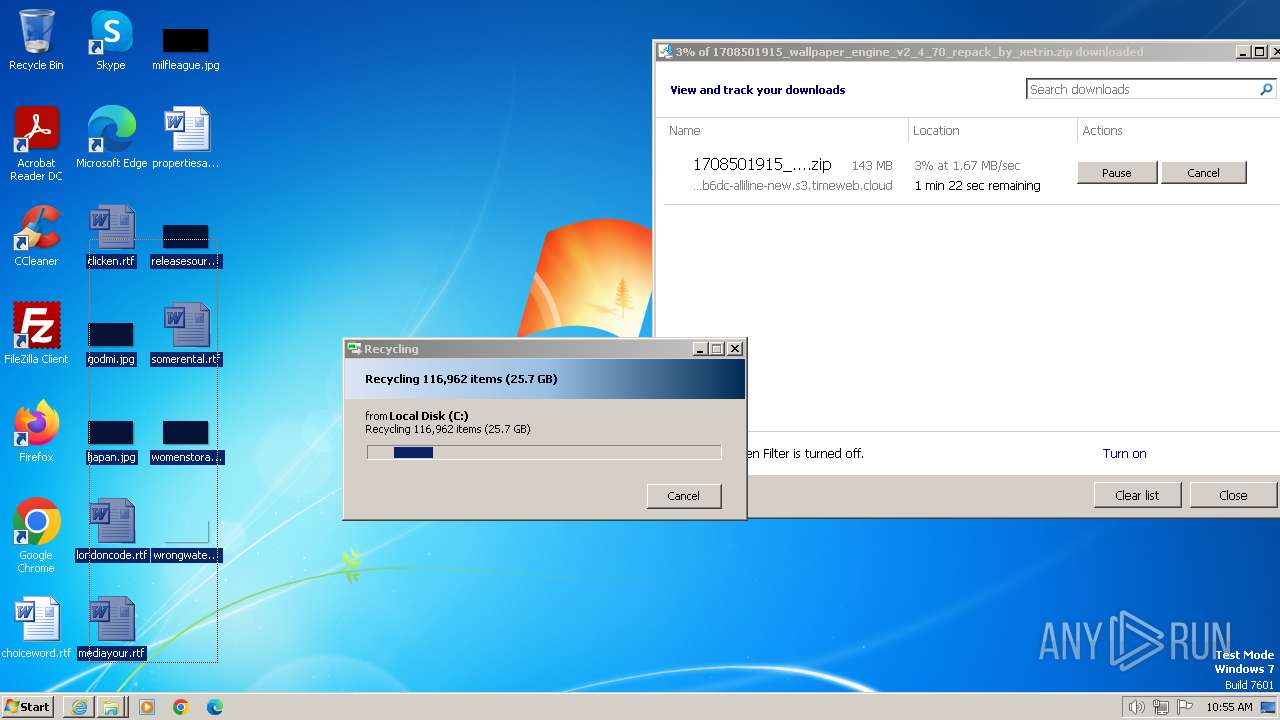
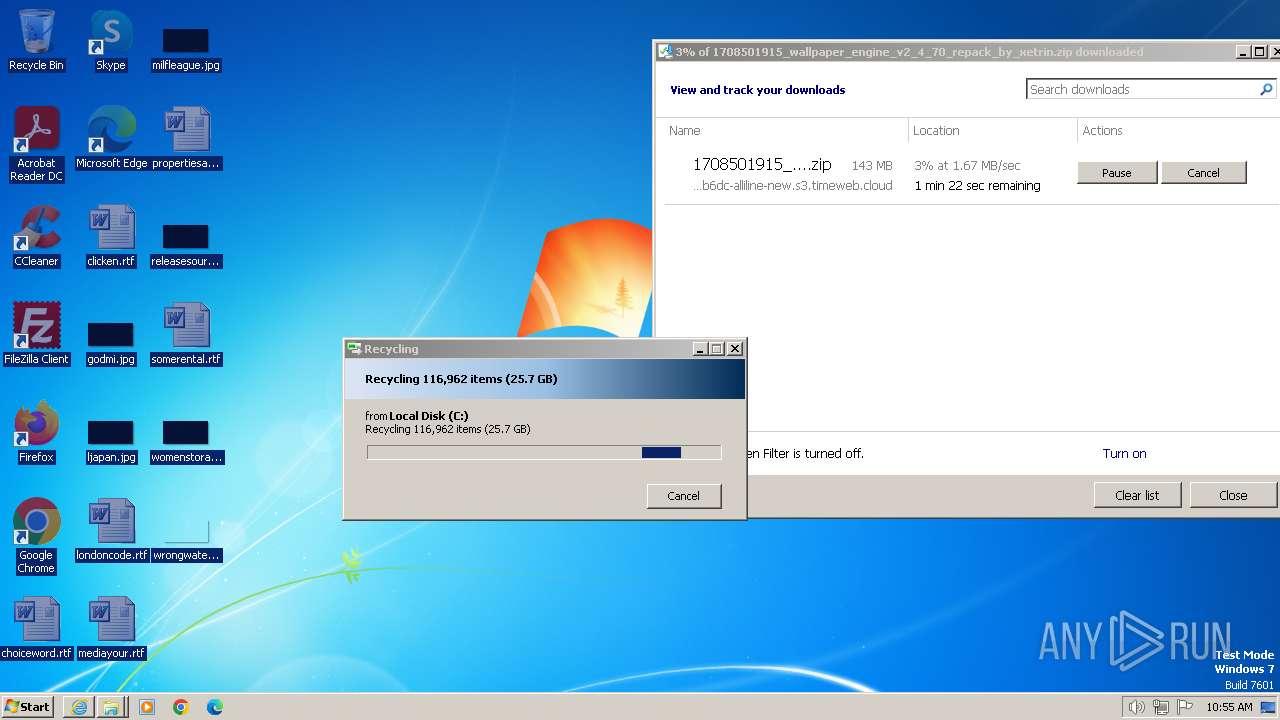
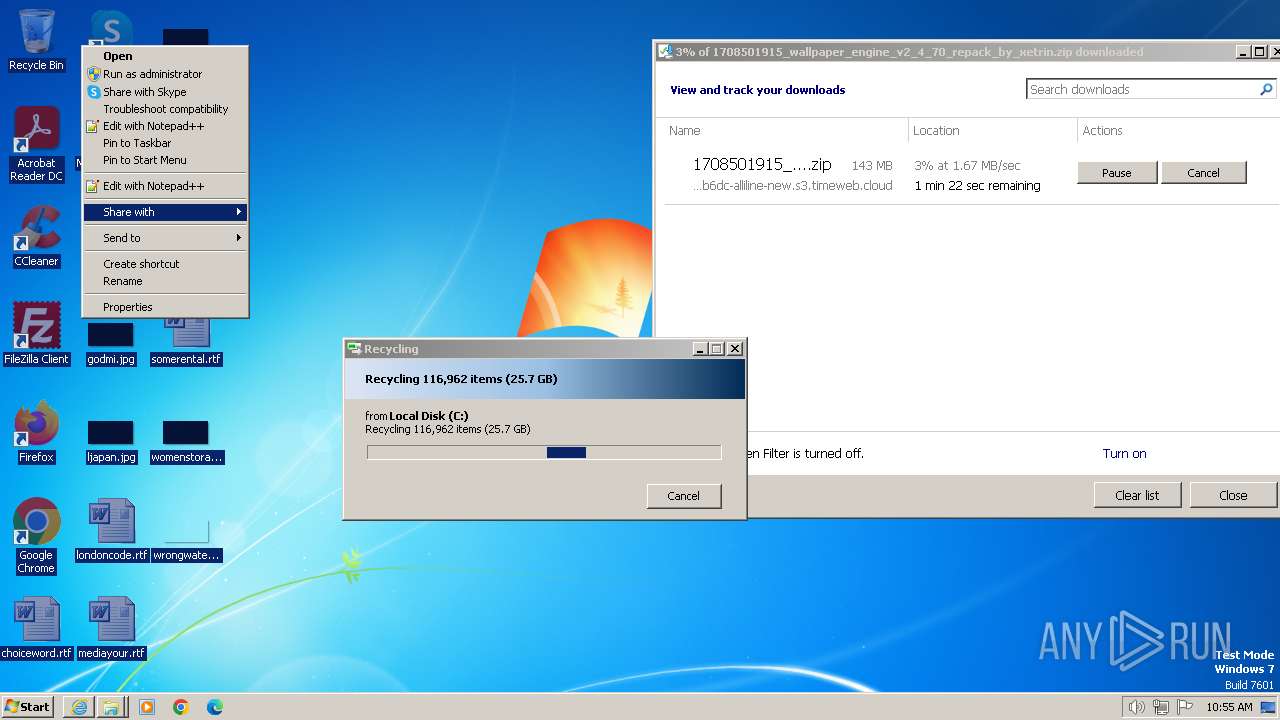
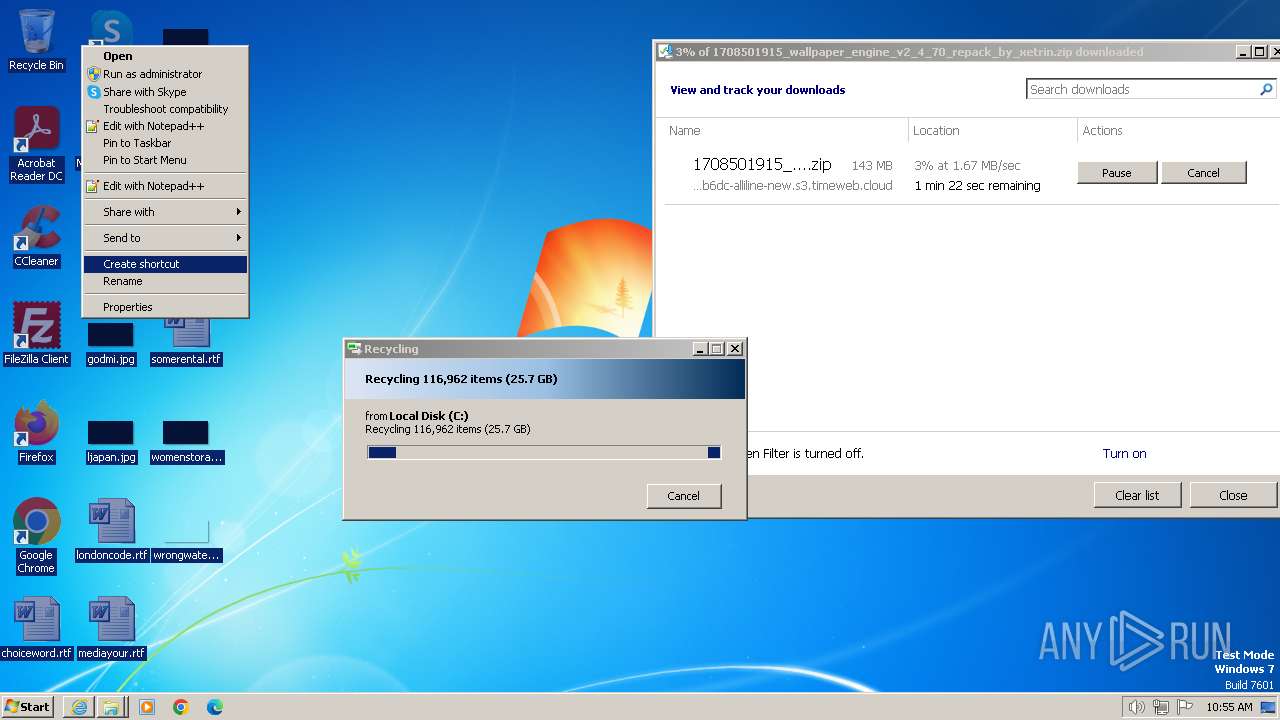
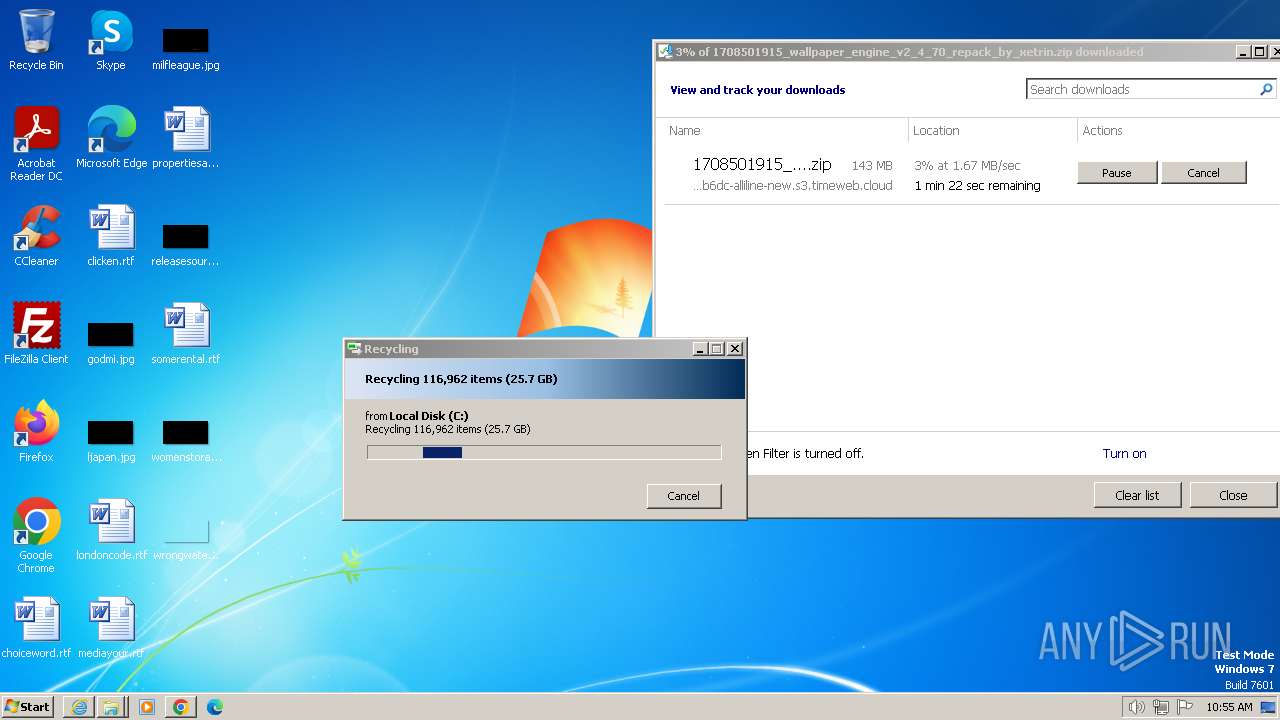
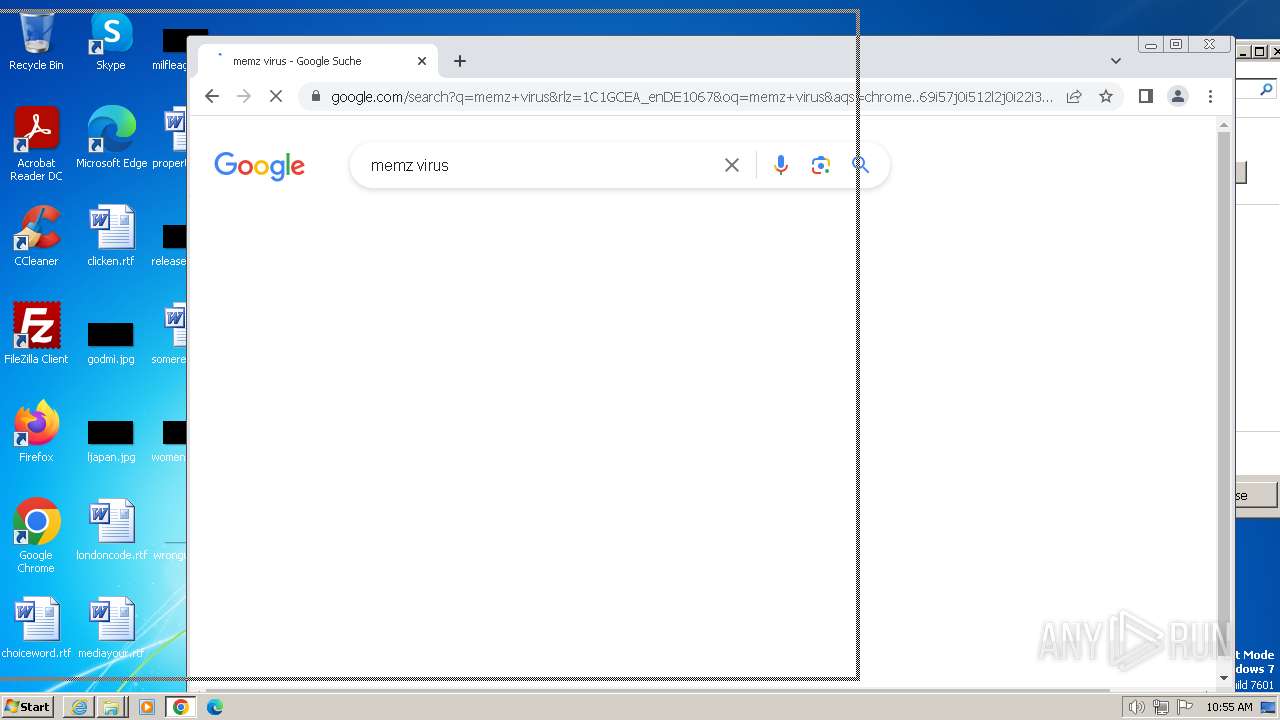
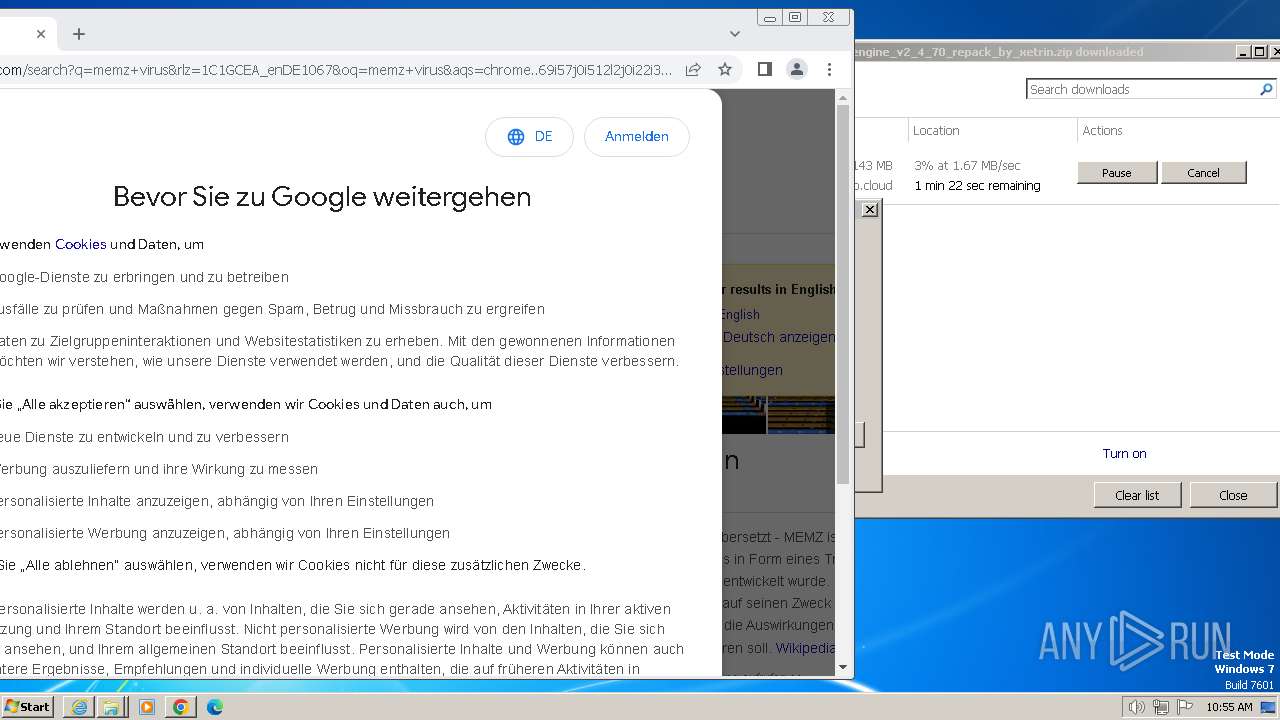
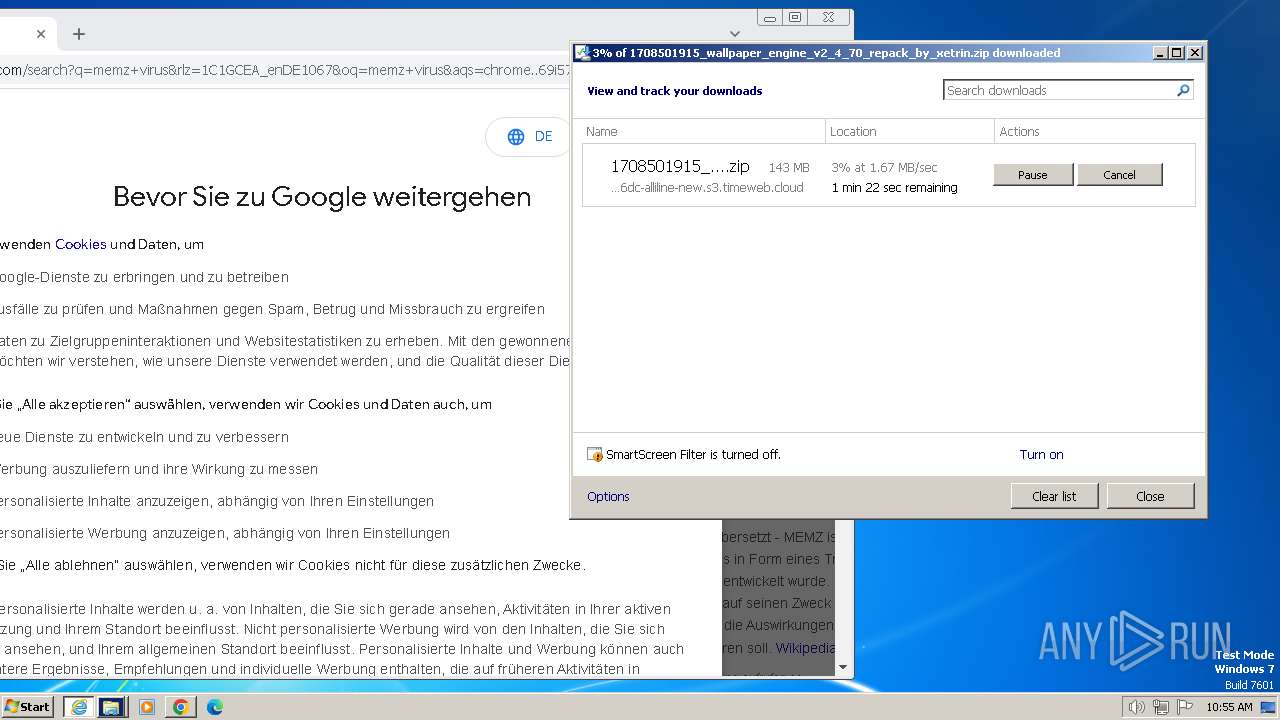
| URL: | https://6bb8b6dc-alliline-new.s3.timeweb.cloud/vsthemes.org/files/2024-02/1708501915_wallpaper_engine_v2_4_70_repack_by_xetrin.zip |
| Full analysis: | https://app.any.run/tasks/1664a51e-c27c-469a-8903-5bc813b53755 |
| Verdict: | Malicious activity |
| Analysis date: | February 26, 2024, 10:53:26 |
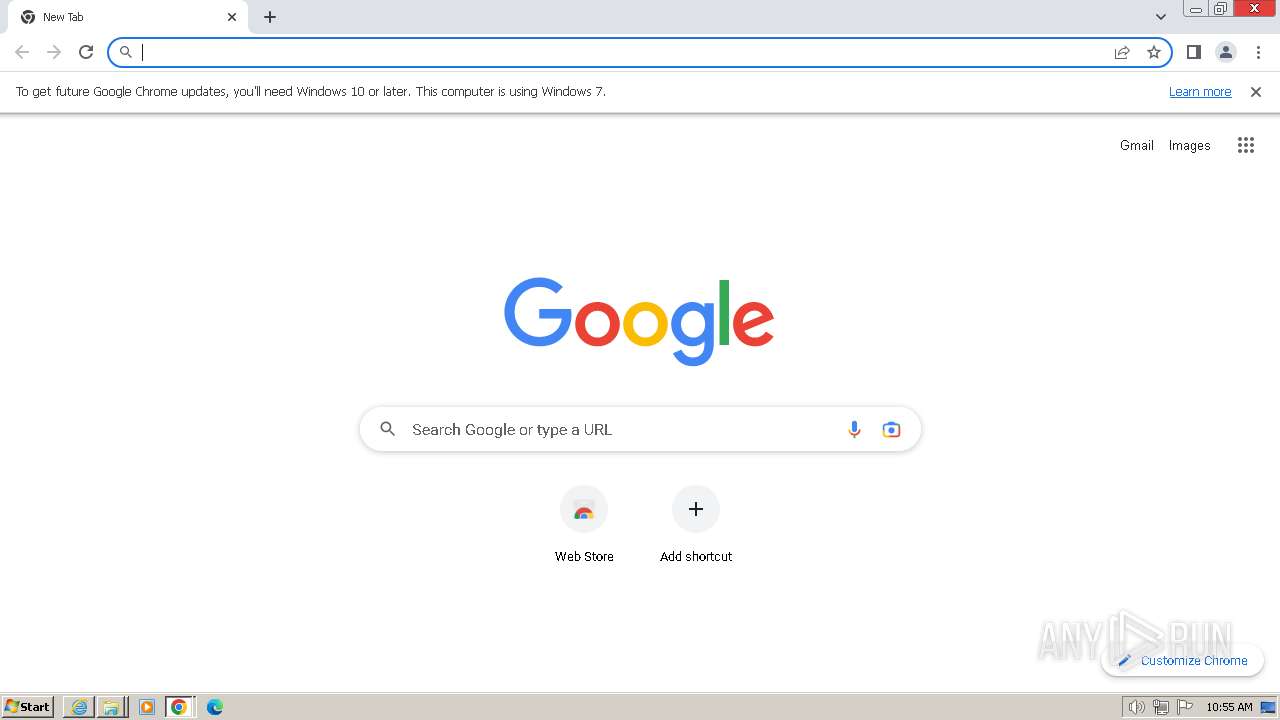
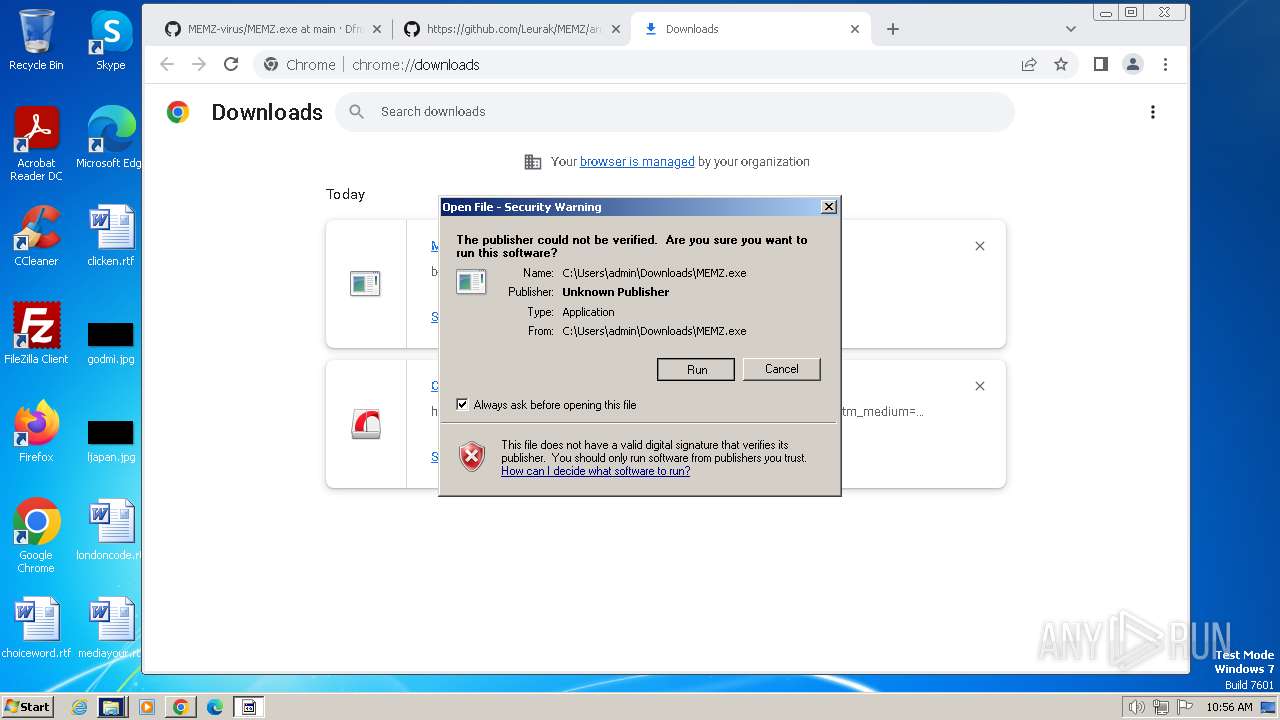
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5348CEAFCFA2DAA152CC9482814EEC31 |
| SHA1: | 5C38B4B2ACC1B4A435AF840791BB97EF8ADA05D7 |
| SHA256: | EBFB173CA458EB237EC869F9A819059B5D0A7422ABFE35576CB36E4C4E82A787 |
| SSDEEP: | 3:N8dd05JJMJK5ASL9ASAHaLBrrMOONXzoaLVdOVyrb66mRutMXU:2dd0ZMwASJASAHmB8OOzo63IotMXU |
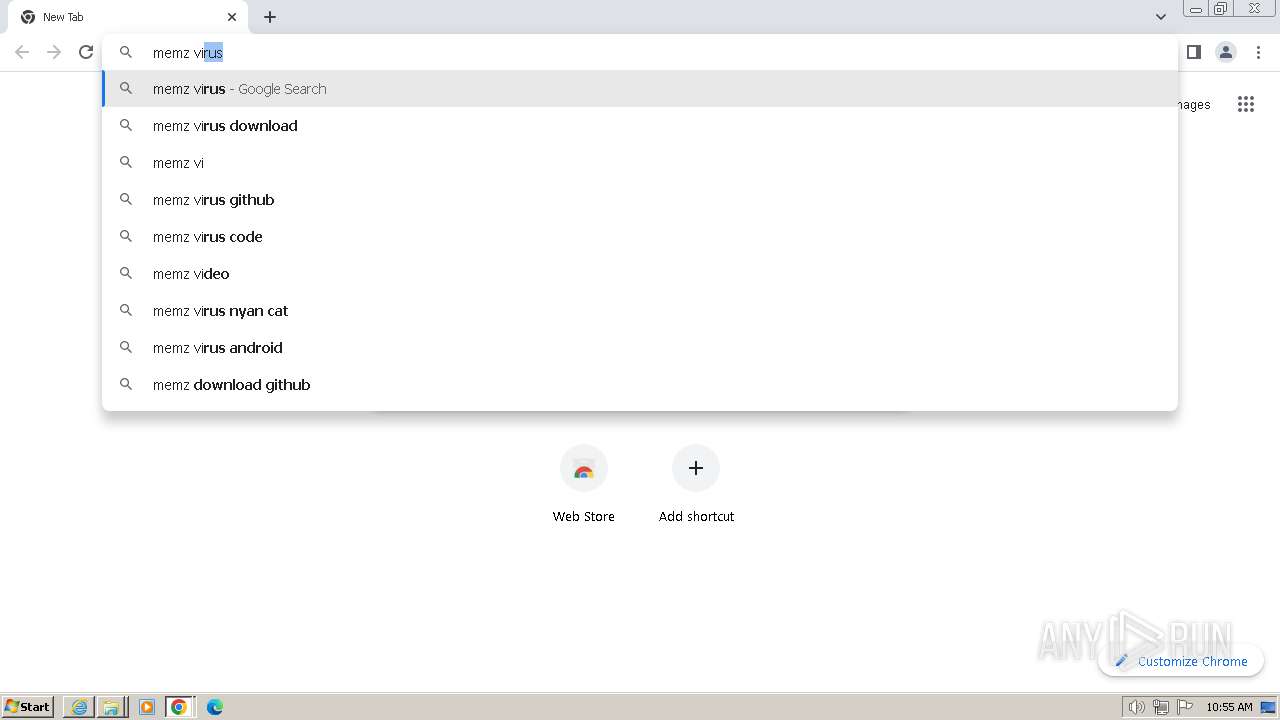
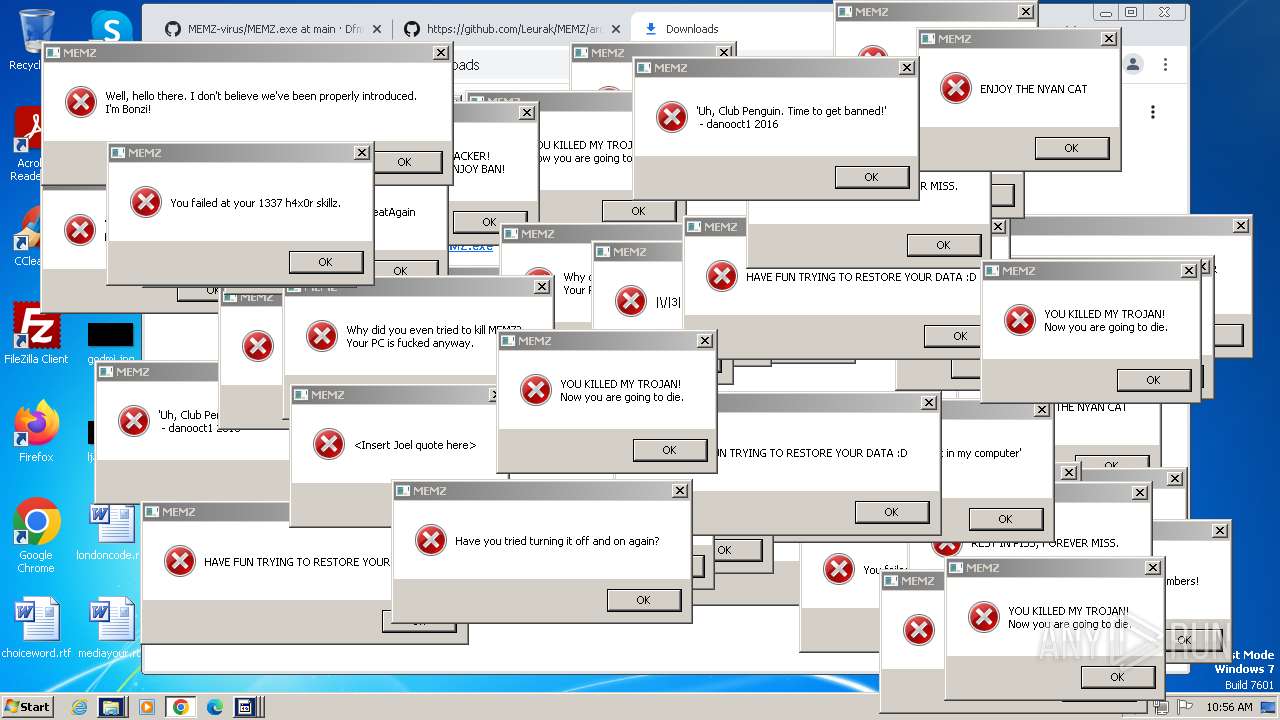
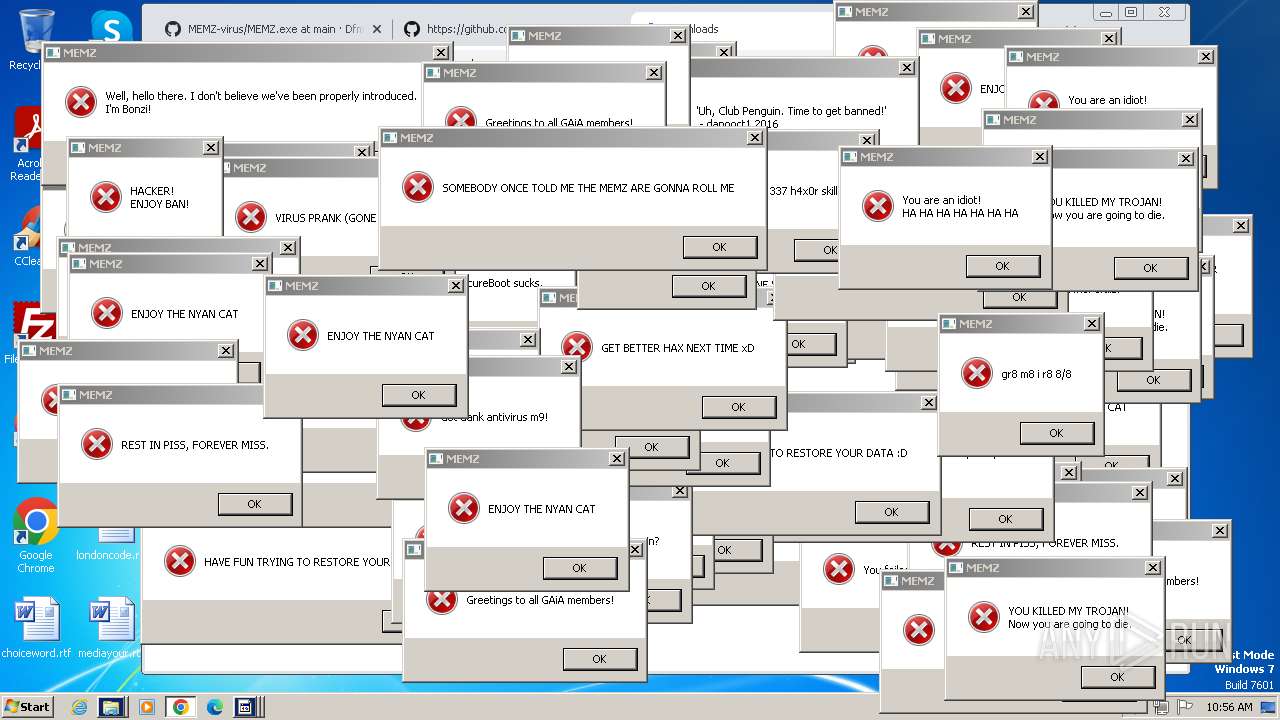
MALICIOUS
Actions looks like stealing of personal data
- dllhost.exe (PID: 3540)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3700)
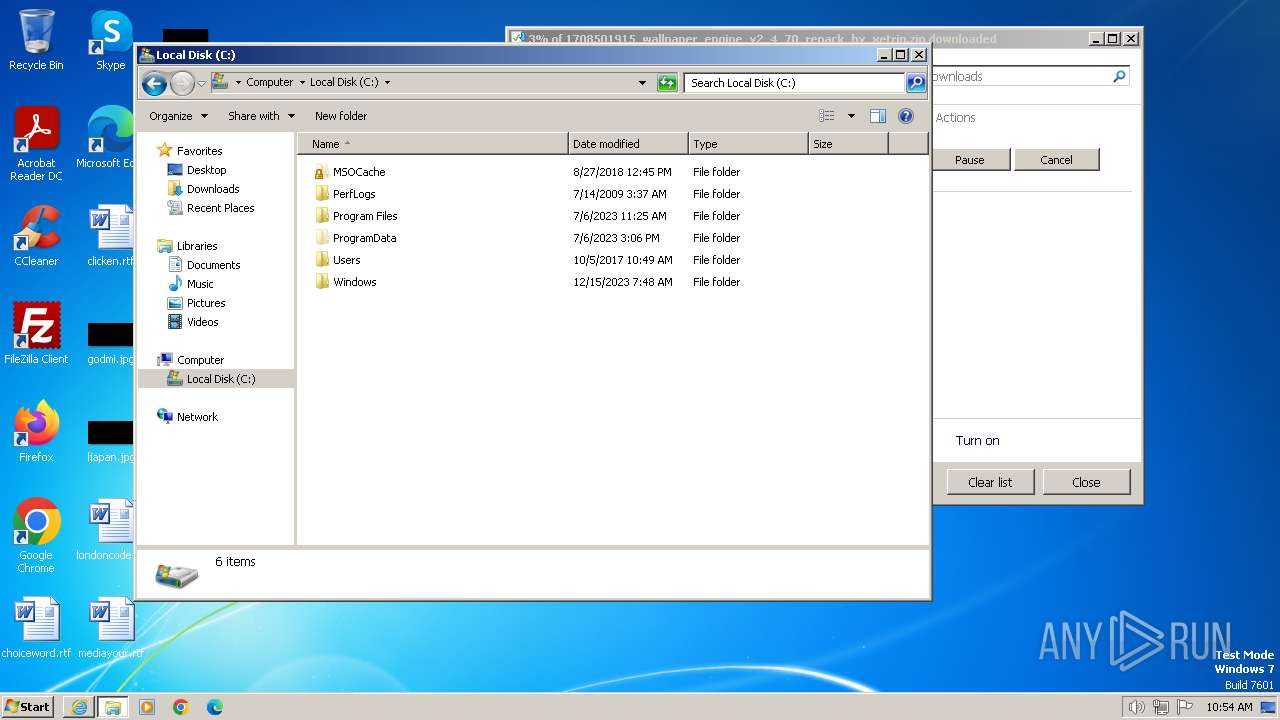
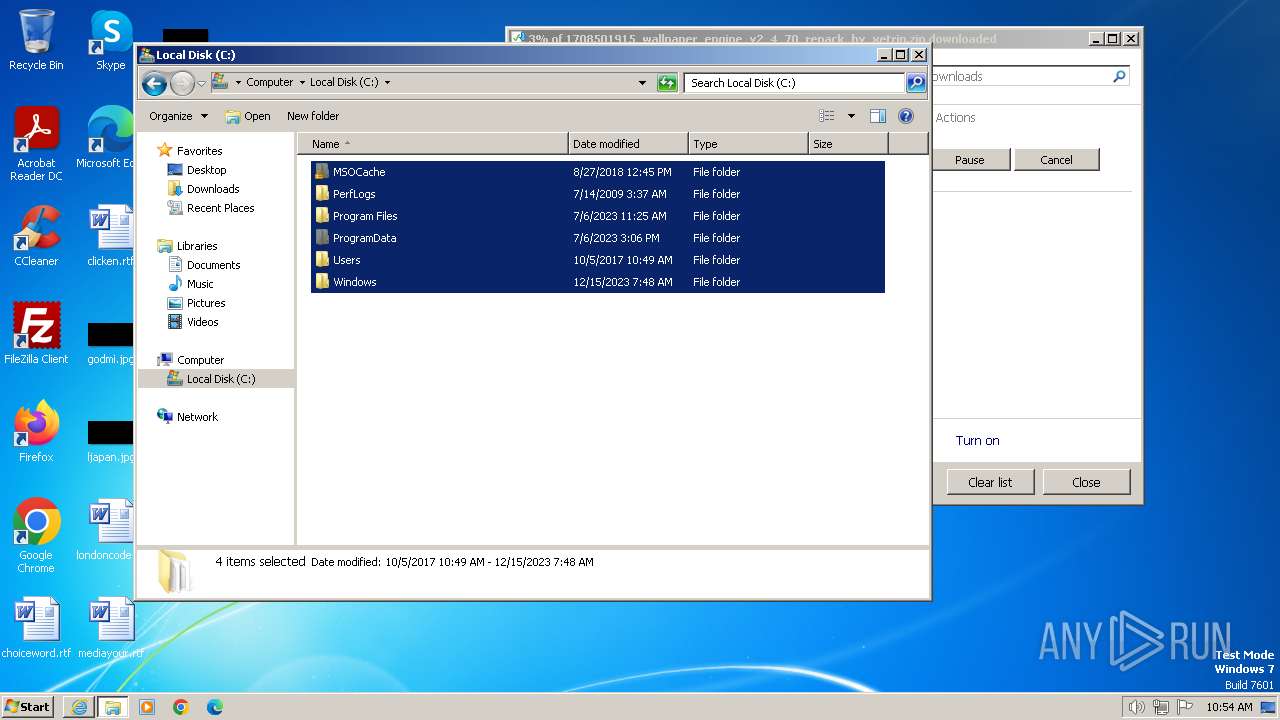
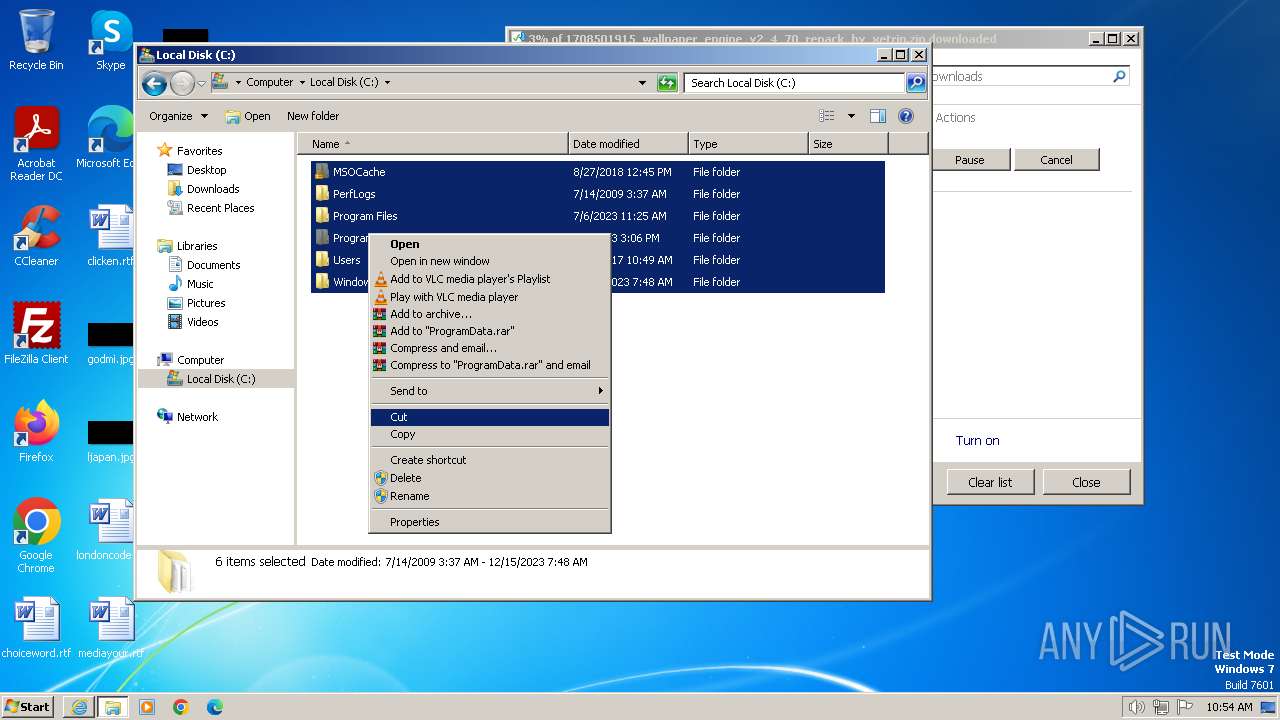
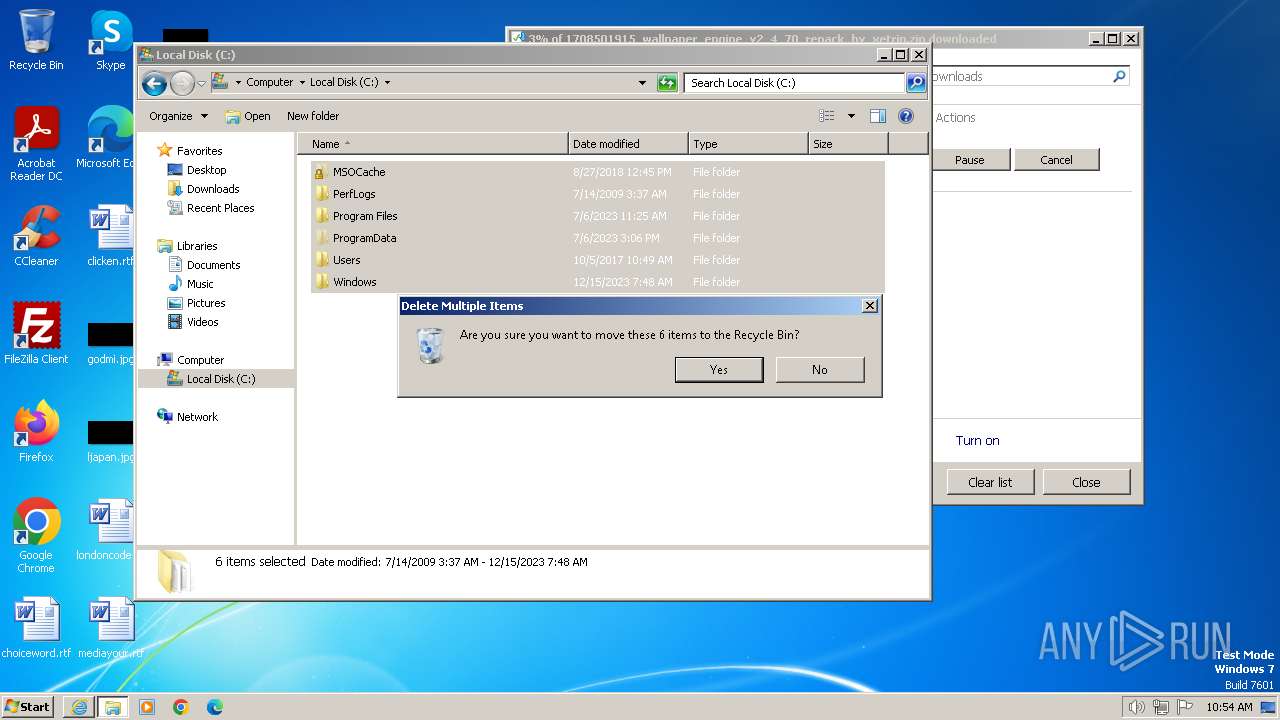
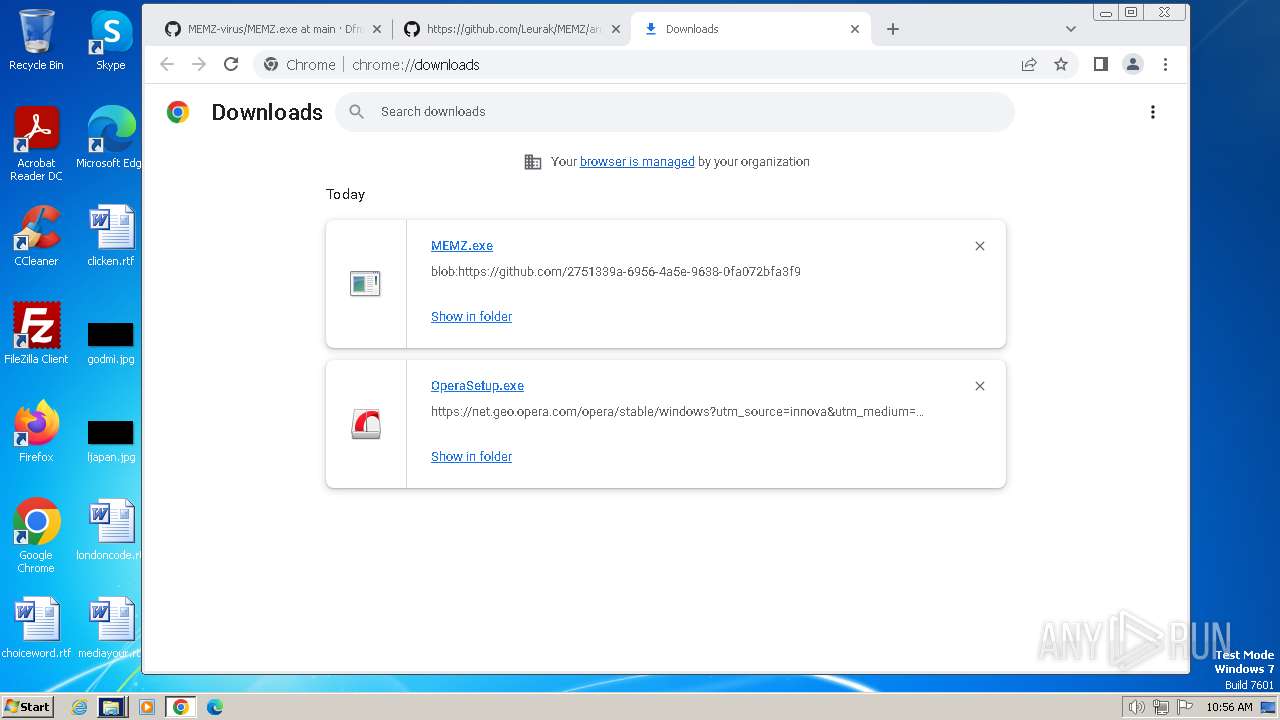
Manual execution by a user
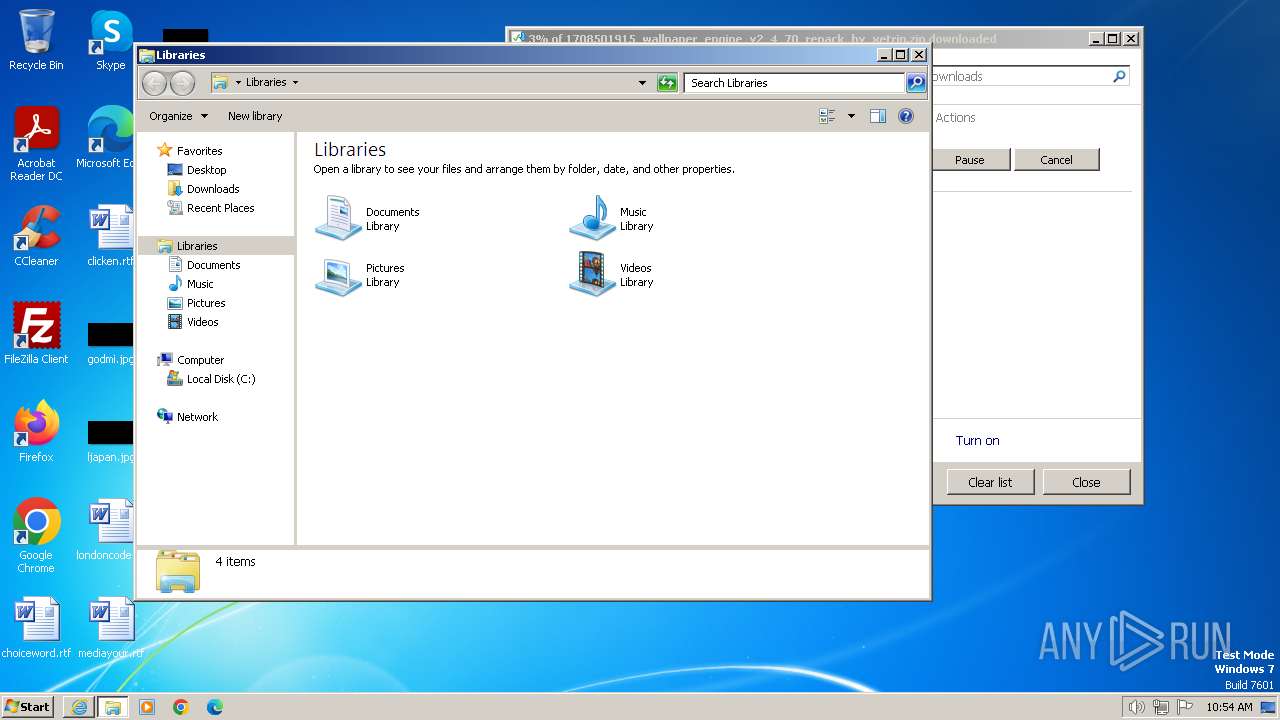
- explorer.exe (PID: 3940)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
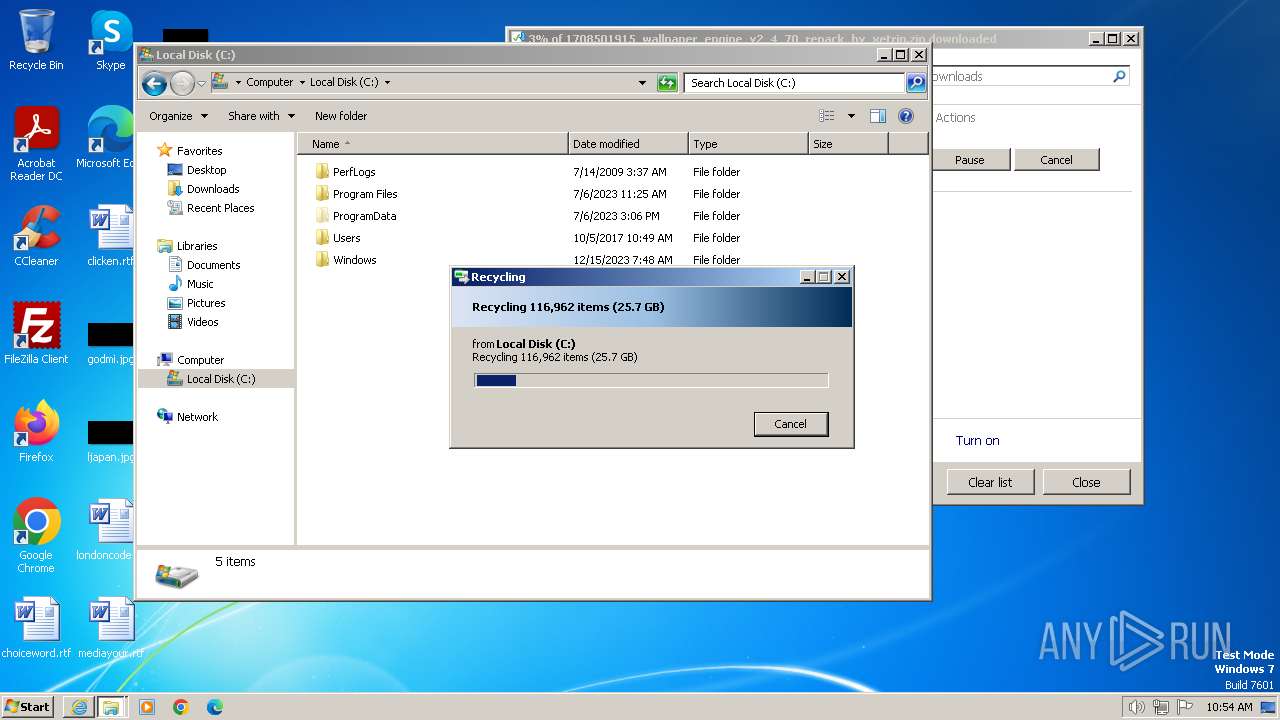
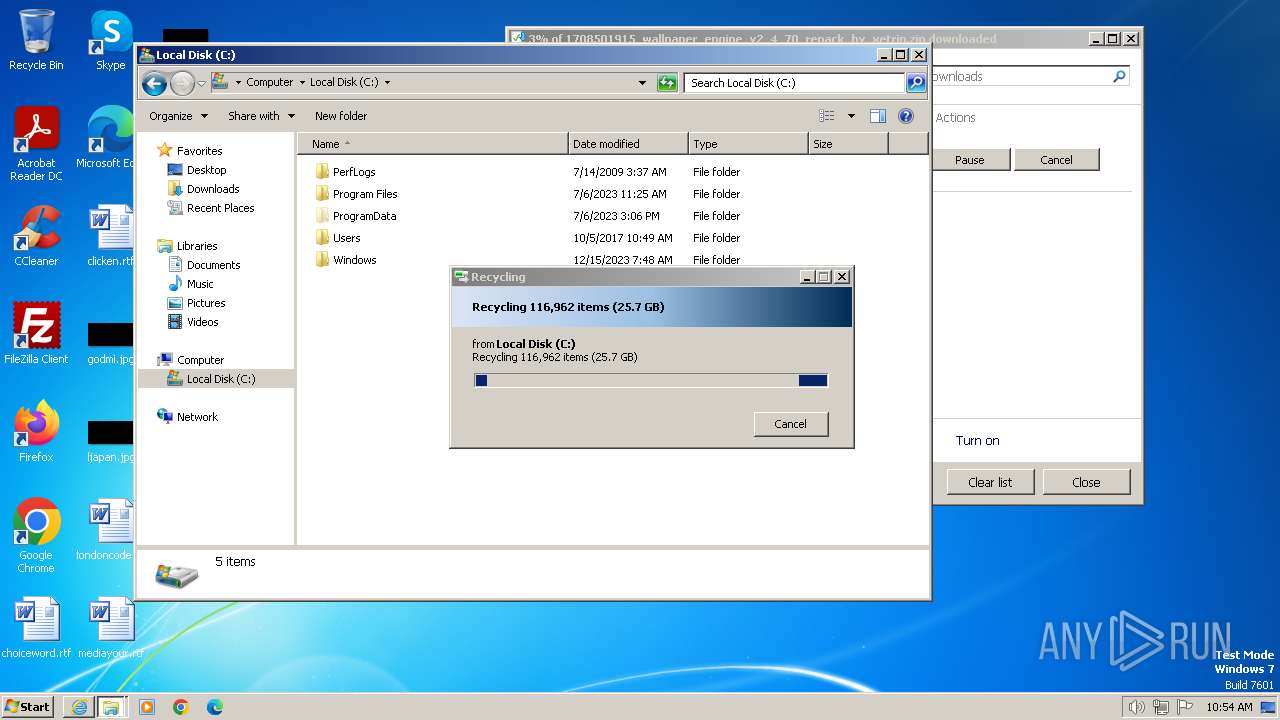
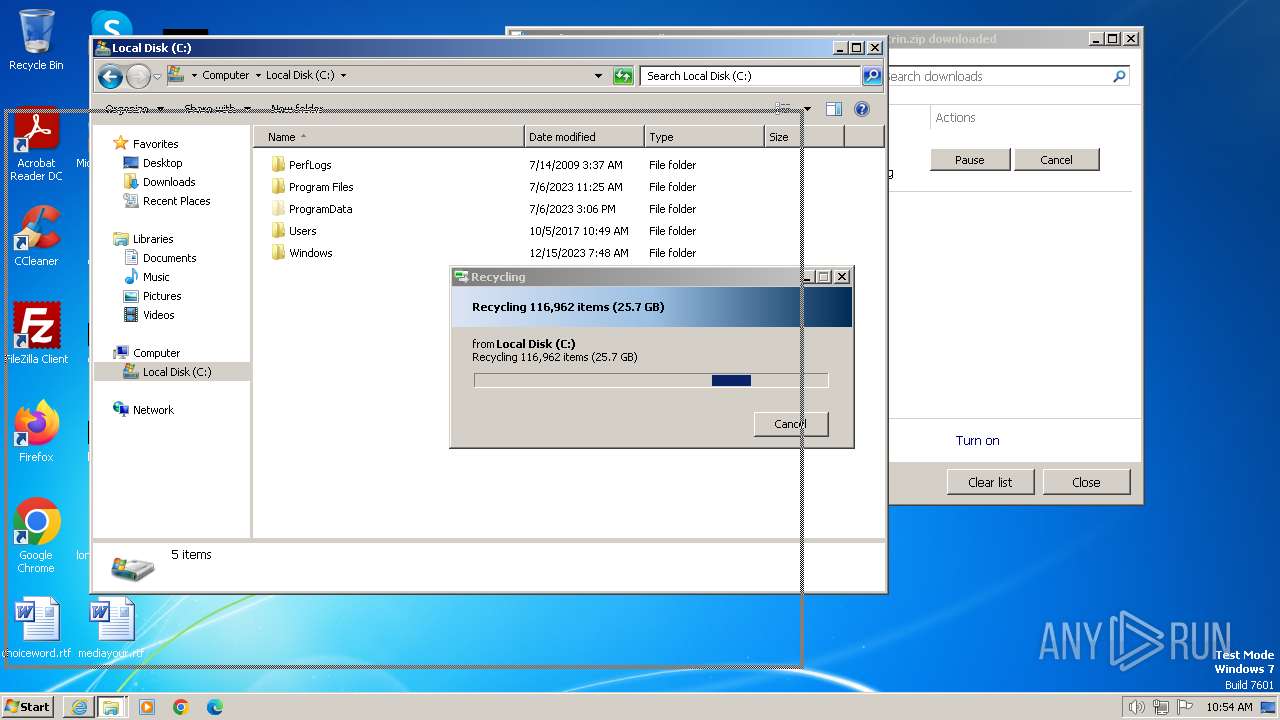
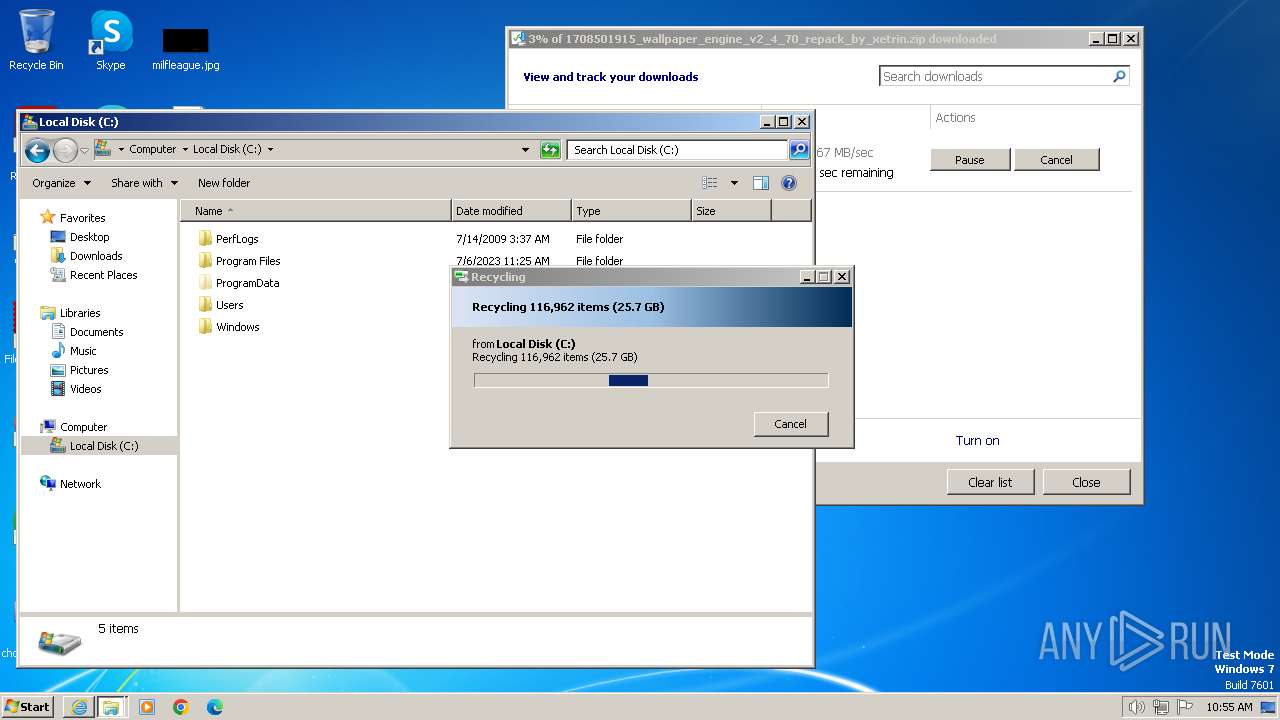
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3700 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://6bb8b6dc-alliline-new.s3.timeweb.cloud/vsthemes.org/files/2024-02/1708501915_wallpaper_engine_v2_4_70_repack_by_xetrin.zip" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3952 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3700 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3940 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3540 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
22 547
Read events
22 435
Write events
84
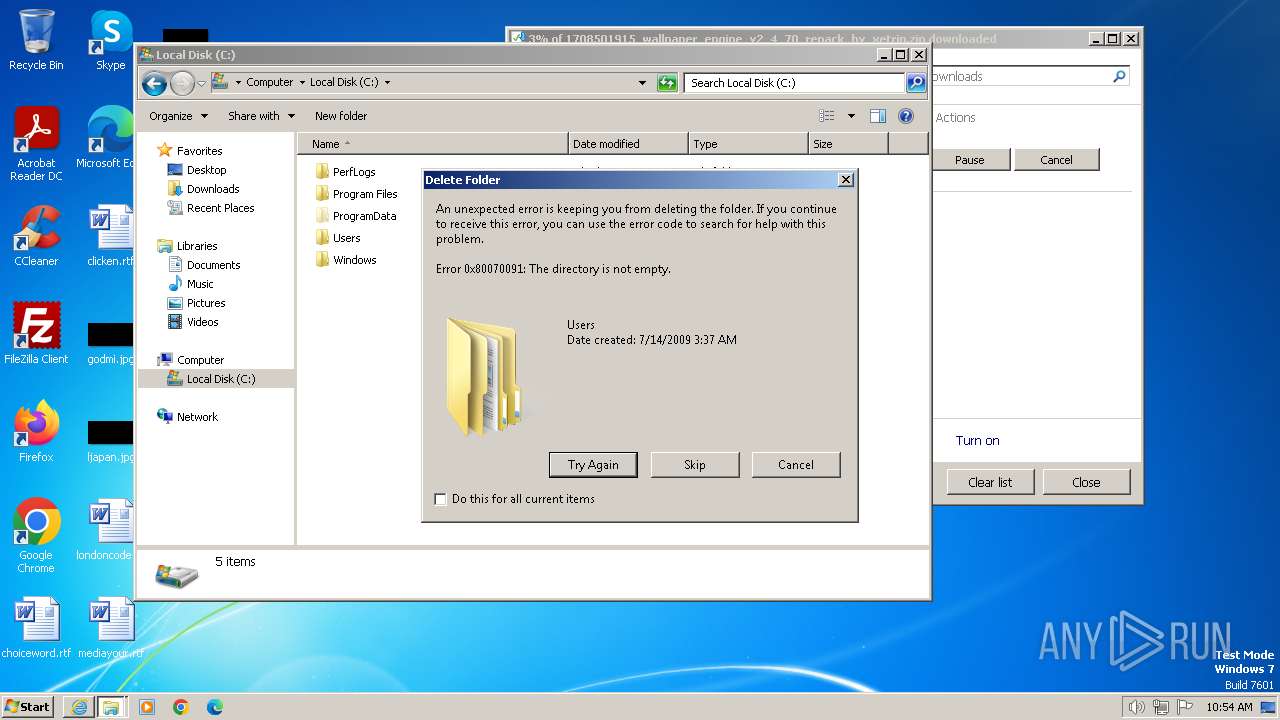
Delete events
28
Modification events
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 206858400 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090850 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 507014650 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090850 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3700) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
14
Text files
12
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver6E07.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3700 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\X3GPZB7X.txt | text | |
MD5:387761C06F9179BDA7BA96DF105678D5 | SHA256:48662A1E9A5CC540AF3D84927D1A76FFBF4ABD8180EF904DF761632D72EAF055 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_005284E085E122BD76B51F33745F7753 | binary | |
MD5:BE73A81AA0784275FE670BD57FE9B94A | SHA256:E4B170E375910192FC33E55A7D1E7C8332DAE2CD8480510C252620E528482176 | |||
| 3700 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\CNEVNCS2.txt | text | |
MD5:30AF532E5C7C09BDB9E05CF2380FCA23 | SHA256:2D4FAD850DEBC7CD64143F72B10BA01CE859E8173B463EA46C3D1B06B32002BA | |||
| 3700 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\15YRVNEA.txt | text | |
MD5:0E3AD85575448130B60AE123281435A0 | SHA256:C06214E3C6F3448D661EE62EBB04BD9F0488FD4555798649AA337B836DEF62B3 | |||
| 3700 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:2C903313F9FBE861F49A0F33CB26266F | SHA256:31838DA700DCA79A28905A515DEB6B23182EAA4E1EC210D20FB150B569C58654 | |||
| 3700 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:F626819807DCA16067EB1429B672C8DF | SHA256:2BDC39689E5AF22316A46B6A4E0A52F1D2E309DB6CA8B03179D6F35472AB826A | |||
| 3700 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\BQEHLX1W.txt | text | |
MD5:C4C29AFE1951412AFEB4D757F15A53AE | SHA256:15B7A6B109A28BBCD0885339F259F7BF9816404790591FB8CA1B70224A5AA87A | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_005284E085E122BD76B51F33745F7753 | binary | |
MD5:CA0EA445FB58FDB560D8B5E27784356A | SHA256:57161C305053910231FC28191F29036591F2DA2981BAAA452633001EBB3396FB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
185
DNS requests
174
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?927e0d673a39dd41 | unknown | — | — | unknown |
3952 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5b0325f31ae0f9b6 | unknown | — | — | unknown |
3700 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?70d85e3b0e586cab | unknown | — | — | unknown |
3700 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9aee5c2adfb08fdb | unknown | — | — | unknown |
3700 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?96c8eb5dfc595a04 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1b8fee253118cbef | unknown | compressed | 65.2 Kb | unknown |
3952 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHe9DgdC1dnp0EnXdNAqb5o%3D | unknown | binary | 1.40 Kb | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?624d1ab720bef5f8 | unknown | compressed | 65.2 Kb | unknown |
3700 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3952 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr3dvtlsca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQoKOHJRQbCE%2B3DXqwFiztBxLYdhwQUDZjAc3%2Brvb3ZR0tJrQpKDKw%2Bx3wCDEr94wZEx68NP6rgBw%3D%3D | unknown | binary | 1.38 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3952 | iexplore.exe | 217.78.234.244:443 | 6bb8b6dc-alliline-new.s3.timeweb.cloud | Ltd Novorossiysk Telecom Company | RU | unknown |
3952 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3952 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | CLOUDFLARENET | — | shared |
3700 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3700 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3700 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
6bb8b6dc-alliline-new.s3.timeweb.cloud |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |